“Ever tried juggling cybersecurity policies while managing a community cloud? It’s like trying to text and drink coffee—inevitably messy.”
In today’s hyper-connected world, community cloud services are revolutionizing how organizations collaborate. But let’s face it: securing access to shared resources isn’t exactly a walk in the park. That’s where cloud secure access comes into play. In this guide, we’ll explore how to implement robust security measures without losing your sanity (or your caffeine supply).
By the end of this post, you’ll understand:
- The challenges of securing community clouds.
- A step-by-step approach to building scalable solutions.
- Best practices that balance usability and safety.
- Real-world examples and FAQs to clear up confusion.
Table of Contents
- Key Takeaways
- Why Cloud Secure Access Matters
- Building a Cloud Secure Access Framework
- Top Tips for Strengthening Security
- Success Stories from Real Users
- Frequently Asked Questions
- Conclusion
Key Takeaways
- Zero Trust Architecture: Adopt a ‘never trust, always verify’ mindset to protect sensitive data.
- Access Controls: Use role-based access control (RBAC) and multi-factor authentication (MFA).
- Encryption: Ensure all communications within the community cloud are encrypted.
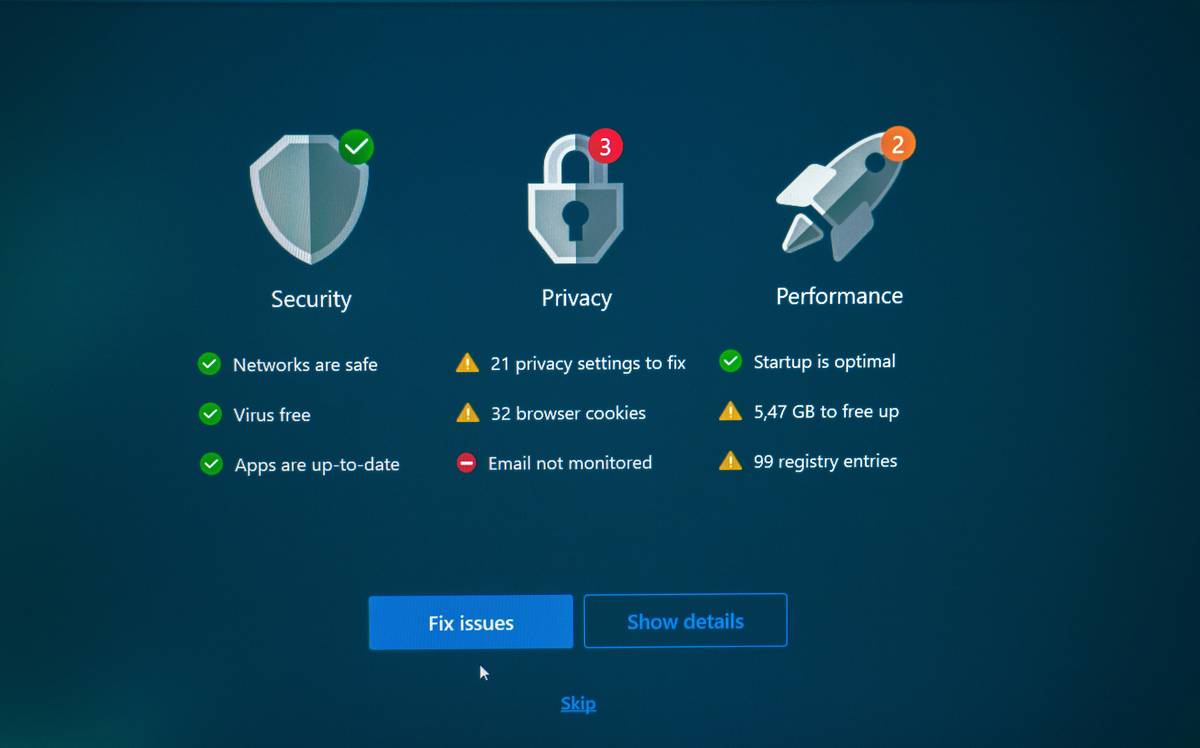
- Regular Audits: Continuous monitoring helps identify vulnerabilities early.
Why Does Cloud Secure Access Matter?
Here’s the deal: A community cloud is essentially a big digital neighborhood. Organizations share infrastructure but keep their individual spaces private. Sounds great—until someone leaves the virtual back door open. Oops!
A personal fail here: I once recommended an organization adopt a basic password policy… only for them to get hacked within weeks because employees reused passwords across platforms. Lesson learned? Weak access controls = ticking time bomb.
This strategy is not just about preventing breaches; it’s chef’s kiss for ensuring compliance with regulations like GDPR and HIPAA. Plus, nobody wants to explain why customer data leaked due to poor planning.
Building a Cloud Secure Access Framework
Optimist You: “We can totally secure this thing!”
Grumpy You: “Ugh, fine—but only if there’s pizza involved.”
Step 1: Define Clear Access Policies
Start by mapping out who needs what level of access. Ask yourself:
- Who are the stakeholders?
- What resources do they need?
- Which actions should be restricted?
Step 2: Implement Role-Based Access Control (RBAC)
This ensures users get access based on roles rather than ad-hoc decisions. For instance:
- Administrators handle high-level tasks.
- Data analysts view reports but don’t modify datasets.
Step 3: Enable Multi-Factor Authentication (MFA)
Add an extra layer of protection so even if credentials are compromised, attackers still can’t log in easily.
Step 4: Encrypt Data at Rest and in Transit
No matter where your data lives or travels, encryption keeps prying eyes away. Tools like SSL/TLS certificates come highly recommended.
Step 5: Conduct Regular Security Audits
Think of audits as oil changes for your car—they prevent bigger issues down the road. Schedule quarterly reviews to patch vulnerabilities.
Top Tips for Strengthening Your Approach
- Don’t Shortcut Password Complexity Rules: Require strong, unique passwords.
- Automate Patch Management: Stay ahead of threats with auto-updates.
- Educate Users: Phishing attempts target people more than systems—train accordingly.
- TERRIBLE TIP ALERT: Don’t skimp on documentation—it’s tempting but disastrous.
Success Stories from Real Users
Rant Alert: One pet peeve? Organizations claiming ‘we’re too small to worry about security.’ Newsflash: Hackers LOVE low-hanging fruit.
Take TechCorp Inc., for example. They transitioned from public to community cloud, implementing RBAC and MFA overnight. Result? Zero incidents over two years despite massive growth.
Frequently Asked Questions
What Makes Cloud Secure Access Different in a Community Cloud?
Unlike public clouds, community clouds require tailored access policies since multiple entities share responsibility.
Is Encryption Really Necessary?
Yes. Without encryption, intercepted communications can expose critical information.
Can Small Teams Afford Advanced Security Measures?
Absolutely—with free tools like Let’s Encrypt for SSL certs and Google Authenticator for MFA.
Conclusion
To sum it up, mastering cloud secure access means blending technical savvy with smart policies. Whether through RBAC, encryption, or regular audits, you’ve got the tools to lock things down tight. So, grab another cup of coffee—you earned it!
Side note: Like finding Waldo in a crowd, securing your community cloud takes patience and persistence. Just remember: slow and steady wins the race.
Your Daily Dose of Nostalgia:
Data safeguards, night and day, Protecting files—the only way. Cloud security—a Tamagotchi, Needs care, love, and rock n’ roll.